A vulnerability is a weak spot in a system. Vulnerabilities enable hackers and crackers to gain access to a network.
It is virtually impossible to have no weak spots, and not all weak spots exist inside the code itself. The biggest vulnerability for many companies is people.
Human examples of vulnerabilities include a human response to phishing emails or weak passwords. Technological vulnerabilities include software that hasn’t been updated or patched, or could exist as a weakness in the source code of a program.
To accurately define what an exploit is, think of the act of the hacker or cracker using a vulnerability to enter or compromise IT systems or software. Exploits need vulnerabilities to exist, which is why preventing vulnerabilities is so important.
In today’s technologically advanced world, criminals don’t need to be sophisticated coders or computer experts to exploit a vulnerability — especially of the human variety. They can buy automated tools to attack weaknesses on a grand scale and there’s plenty of data available on the dark web to trick your team into making a mistake and letting them in.
View all FAQs
A zero day attack happens when a hacker takes advantage of an unpatched or previously unknown vulnerability for the first time (also known as a zero day vulnerability). Some examples of zero day exploits include: Critical system vulnerabilities and exposures are tracked by some organizations and websites to distribute to others. They maintain lists of…
There are multiple benefits associated with IT service management, including: Aside from the benefits above, the day-to-day conveniences of using an ITSM are many. ITSM is not just support via a help desk or a service desk. While an ITSM may support your business via a service desk, the offerings are much broader than that….
An IT service management (ITSM) company uses a process to create, deliver, plan, support, implement and operate your IT technology to best serve you and your clients or customers. Their services encompass all technology services and devices: laptops and the applications on them, servers, printers, all software applications, even your passwords. Here’s a list of…
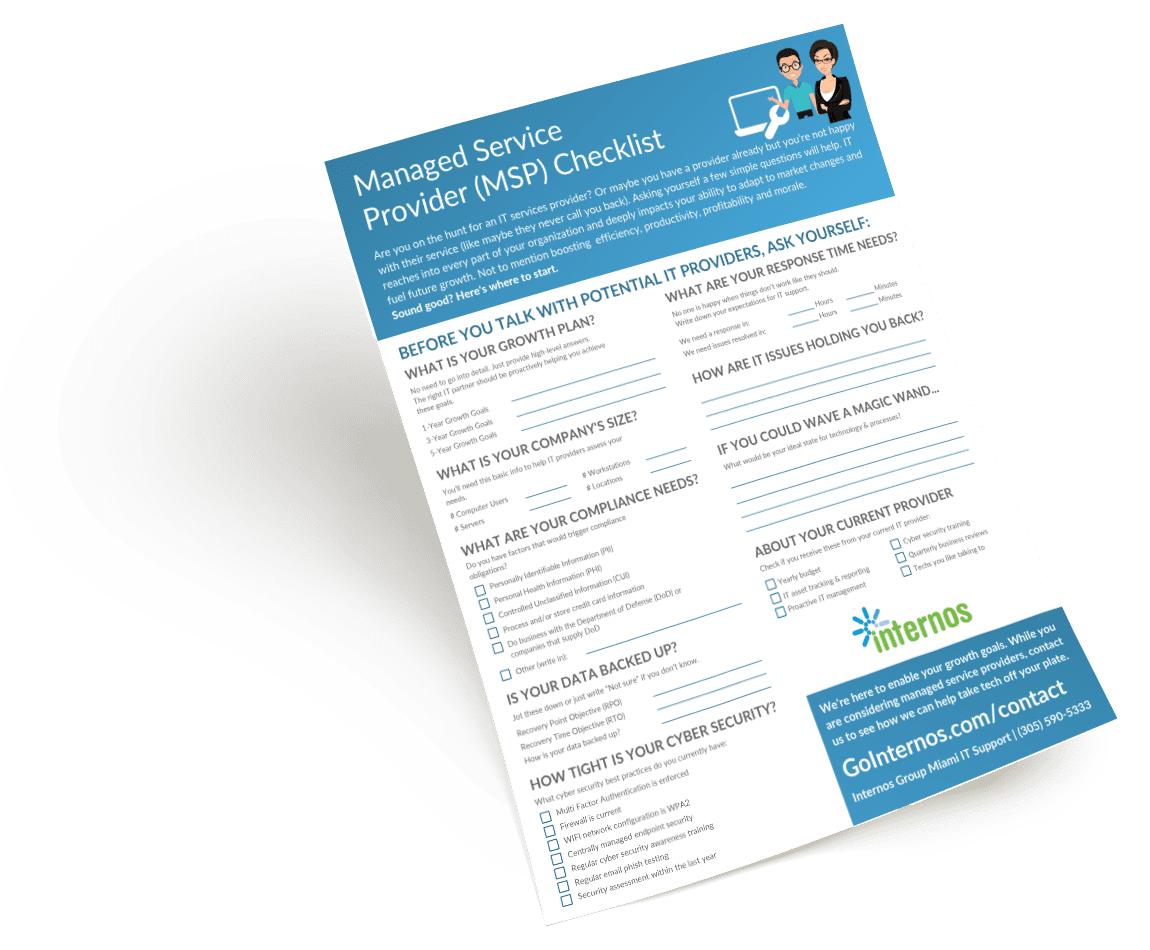
Use our Checklist to Find the Right IT Support
Are you a first-timer to IT support? Maybe you aren’t happy with your current MSP? Our easy-to-follow checklist can guide you through the process of the best IT services provider for your business. It will help you help you outline and define:
- Your business goals for the next few years
- The stats that potential MSPs will need to work out a plan for your company
- The risk areas in your backup and cyber security practices
- What you expect from your IT support provider
- And more!