FAQ: Common Business IT Questions
IT FAQs & Answers
If you’re looking for the right IT support services for your Miami or Fort Lauderdale area business, we know that you’ll have plenty of questions. So, we’ve pulled together the most common business IT questions and answers. Of course, we’re happy to discuss your specific IT questions, too. Just book a meeting for a no-pressure consultation with one of our IT experts.
Until then, we hope you find these business IT questions and answers helpful.
What Is a Vulnerability vs an Exploit?
A vulnerability is a weak spot in a system. Vulnerabilities enable hackers and crackers to gain access to a network.
It is virtually impossible to have no weak spots, and not all weak spots exist inside the code itself. The biggest vulnerability for many companies is people.
Human examples of vulnerabilities include a human response to phishing emails or weak passwords. Technological vulnerabilities include software that hasn’t been updated or patched, or could exist as a weakness in the source code of a program.
To accurately define what an exploit is, think of the act of the hacker or cracker using a vulnerability to enter or compromise IT systems or software. Exploits need vulnerabilities to exist, which is why preventing vulnerabilities is so important.
In today’s technologically advanced world, criminals don’t need to be sophisticated coders or computer experts to exploit a vulnerability — especially of the human variety. They can buy automated tools to attack weaknesses on a grand scale and there’s plenty of data available on the dark web to trick your team into making a mistake and letting them in.
What Is a Zero Day Attack?
A zero day attack happens when a hacker takes advantage of an unpatched or previously unknown vulnerability for the first time (also known as a zero day vulnerability). Some examples of zero day exploits include:
- A known vulnerability that had never been previously exploited.
- New or undetected malware.
- A previously unknown vulnerability that is exploited.
Critical system vulnerabilities and exposures are tracked by some organizations and websites to distribute to others. They maintain lists of these and then release patches that will fix them. Once the weakness in the software is patched, it is no longer considered a zero day vulnerability.
It is important to note that sometimes, vulnerabilities are only discovered once people figure out how to exploit them. Other times, the vulnerability is known (hypothetically) but it is not known how that vulnerability could possibly be exploited. This is why there is often a gap or delay between when a zero day vulnerability is discovered and when a zero day attack occurs.
Your average antivirus and anti-malware software can only seek out what they know for certain is out there, therefore, they cannot protect against zero day attacks and vulnerabilities.
What Are the Benefits of IT Service Management?
There are multiple benefits associated with IT service management, including:
- Adapting to your needs.
- Enabling teams to share knowledge.
- Helping to prevent breaches and planning strategies for natural disaster situations as well as criminal ones.
- Improving efficiency, service and customer satisfaction.
- Reducing IT costs (by removing redundant or obsolete assets), risk factors and downtime when breaches occur.
Aside from the benefits above, the day-to-day conveniences of using an ITSM are many. ITSM is not just support via a help desk or a service desk. While an ITSM may support your business via a service desk, the offerings are much broader than that.
ITSM processes all service requests whether they are a recurring problem (this application is stuck again), a change to the system (I need to add, remove or modify the database), requests for a new piece of equipment (I need a new computer) or an incident that affects the system (my computer is down).
Note: there is often confusion as to what “service desk” or “help desk” mean especially since these terms vary in meaning from one company to the next. With ITSM, it truly doesn’t matter. All you have to do is call or submit a “ticket” and the issue will be resolved.
What Is IT Service Management?
An IT service management (ITSM) company uses a process to create, deliver, plan, support, implement and operate your IT technology to best serve you and your clients or customers. Their services encompass all technology services and devices: laptops and the applications on them, servers, printers, all software applications, even your passwords.
Here’s a list of what an IT service management company does for your business:
- Advises you on the best type of backup to handle any possible breaches to your data, whether they arise from natural disasters or criminal action
- Assures that access to your company data is exclusive to an authorized current endpoint user (staff, client, etc.). The ITSM will purge the system of former employees or clients who can still get into your network because someone forgot to block their access when they left the company
- Checks your cybersecurity process and plans and reinforces them, or replaces them with ones that are safer
- Examines every application, every endpoint (computer, phone, scanner, etc.) to assure it is up to date, and update them if they are not
- Streamlines your infrastructure to better deliver the high-quality internet technology needed for your business
Ultimately, ITSMs take responsibility for all workplace technology so you don’t have to. They achieve this by building and implementing technology, enforcing the right process for your company, educating your staff about the technology and sticking to the process, and re-educating coworkers when necessary.
What Is the CIS Checklist?
The Center for Internet Security (CIS) is a nonprofit devoted to helping people, businesses and governments protect themselves from cyber threats. It is globally recognized for developing the best practices for securing IT systems and data. The CIS distills advice into a recommended set of actions. These are called the CIS Critical Security Controls. Internos Group created a CIS Checklist as a simple and easy way to see where your company stands in implementing the CIS critical controls.
The CIS Critical Security Controls define the 18 must-have controls to help companies defend against cyber attacks. It focuses attention and resources on additional risk issues that are unique to each business or mission. The controls were determined with input from experts from every sector of business.
The CIS Controls are not not a replacement for any existing regulatory, compliance or authorization scheme. They map to most major compliance frameworks and have been defined for these other frameworks to give a starting point for action.
There could be a lot more than 18 controls, but the consensus was that these 18 actions can thwart the majority of known attacks today. They provide the framework for automation and systems management that should serve cyber defense in the future.
The CIS Controls are updated and reviewed through an informal community process. Government, industry and academic participants each bring deep technical understanding from across multiple viewpoints (e.g., vulnerability, threat, defensive technology, tool vendors, enterprise management) and pool their knowledge to identify the most effective technical security controls needed to stop the attacks they are observing.
Still Not Sure What the CIS Checklist Is?
Sorting through best cyber security practices shouldn’t distract you from your “real job.” If you need assistance in implementing CIS Controls at your business, we’re here to help. Contact us or book a meeting.
What are Dark Web Monitoring Services?
Dark Web Monitoring Services are regularly scans the Dark Web for credentials belonging to you, your employees or your business. Internos offers Dark Web monitoring as well as a free preliminary scan so that businesses can see how the service works and the value it provides.
At Internos, we use a combination of human and sophisticated Dark Web intelligence software to find, identify, analyze and proactively monitor the Dark Web for any of your organization’s employee and customer data. Dark Web Monitoring Services include but are not limited to:
- Hidden chat rooms
- Private websites
- Peer-to-peer networks
- IRC (internet relay chat) channels
- Social media platforms (e.g., Facebook)
- Black market sites
- 640,000+ botnets
One of the things we find is that employees often use the same password for multiple services, exponentially increasing the potential damage from a single compromised credential. This is a green flag to bad actors who steal the information and use it for their monetary gain.
Let Internos help you find and correct those weaknesses before they become threats, attacks or ransom requests. Request a free Dark Web Scan.
What is a Dark Web Scan?
A Dark Web Scan is pretty much exactly what it sounds like, a scan of Dark Web sites for any credentials identified as belonging to your business. The idea is to find credentials that have been compromised so that they can be replaced. Also, it’s important to know what information is out there about your business and employees to keep people from being tricked by phishing or other attempts to breach your cyber security.
The dark web is made up of communities. Some might be legitimate but an estimated 50 percent or more are used for criminal activities. When there is a data theft or breach, the Dark Web is where that data is posted or sold. That means emails, passwords and other digital credentials are available to criminal organizations looking to exploit them.
If you have never run a scan, you might not even know that your company’s and employees’ credentials have been posted there. That leaves you vulnerable. Internos offers a free Dark Web scan as well as ongoing Dark Web monitoring.
How do I roll out a multi-factor authentication set up for my business?
You know MFA is the right move for your business. But how do you smoothly roll out a multi factor authentication set up for your team? As with any change, there will be some resistance. Here is an action plan to help you push past people’s fear to get up and running.
- Start with the IT team, whether it is an internal team or an MSP. Set the goal of rolling out MFA across your networks and systems for all users.
- Include training and support. The rollout plan should include end-user training and support for the entire team. You want to roll out MFA without stressing your team or impacting productivity. The only way to do that is with empathy and training. People using MFA for the first time will feel a bit like learning a foreign language. Training will help them understand why it is important. Ongoing support will help them become comfortable with the new protocols.
- Include your vendors and partners. Each should be required to enable MFA as well. Consider switching vendors if any don’t offer MFA security.
- Monitor invalid access attempts. This data can be used to improve your cyber security.
- Plan for immediate lockout support. People who are locked out or unable to authenticate should get the help they need fast, otherwise people will try to “work around” the system. Lockout support will help ensure that your MFA rollout has as little impact as possible on productivity.
You don’t have to go it alone. Many small and medium sized businesses need help with multi factor authentication set up from a trusted IT partner. Even companies with in-house IT teams find it helpful to have an MSP train teams and monitor access attempts.
For this or any other business IT questions, contact us or book a meeting. We’re here to help.
What is multi factor authentication vs 2 factor authentication?
Multi factor authentication (MFA) and two factor authentication (2FA) are often used interchangeably, but they are technically different. Both prove you are who you say you are when you are logging into a system. But 2fa specifically requires two forms of authentication. MFA requires two or more. So all 2FA is MFA but not all MFA is 2FA.
To understand multi factor authentication vs 2 factor authentication, think of your last login. You were asked to provide a username and password — together these are one factor of authentication. Then you may have been asked for one more factor, such as answers to previously asked security questions. That was 2FA.
All of the factors in the 2FA example fall into the “something you know” category. Most MFA requires you to provide either “something you have” or “something you are.” Here are examples of both:
- “Something you have” is usually your cell phone. When you log in, the system sends you a text or push notification with a code and the system provides a screen to supply the code and complete your login. Text and push notifications are good, but using an authenticator app or token device to receive your code is even better. But all provide an additional layer of security over simply providing information.
- “Something you are” is usually a fingerprint scan, face scan or other form of biometrics.
So don’t worry too much about the terminology: multi factor authentication vs 2fa. What matters is that you use these more robust authentication methods to protect your business.
How do I find top managed IT services providers?
Managed IT service providers come in all shapes and sizes, from the “guy in his garage” to large national firms. So, finding one won’t be a problem. But you can’t just choose any managed service provider. It’s important to find a quality IT partner for your business Here is what to look for:
- 24/7/365 monitoring and support
- Fast response times (e.g., “We’re working on it”) and reasonable resolution times (e.g., “We’re done”) based on the level of impact the issue is having on your business
- Experience with your business, industry, environment and/or requirements — and client references to back it up
- High average customer satisfaction ratings (CSAT) and client references to back them up
- Actually located within the Miami or South Florida area (not simply a local address to attract businesses). Your MSP should provide services in your offices when needed and not just remotely. Even better, they’ll schedule regular onsite visits to train staff or review equipment.
- No long-term contracts. A top MSP doesn’t need to lock you into a long-term contract because they will earn your business month after month with exceptional service. You should be able to cancel all or part of your IT services with 30 days notice.
These are just the basics, but they should help whittle down your list. Then you need to learn about each potential MSP’s specific IT processes and protocols. Get more questions to ask or download our Choose IT Support checklist.
Do I need cyber security assessment services?
Cyber security assessment services are performed to find and fix cyber security risks. There are many types of assessments. Which you need for your business depends on your type of business, your industry, the size of your company and your risk tolerance. But every business should complete cyber risk assessments of some type.
The most common services include:
- Vulnerability assessment. Like the name suggests, this test finds potential weak spots inside and outside your network.
- Penetration test, aka, a simulated cyber attack. Authorized cybersecurity experts (“white hat hackers”) try to breach your system. These tests are much more involved and expensive so they are rarely needed by small businesses.
- Network audit, which looks at what is on your network, often finding unauthorized software or hardware as well as performance or licensing issues.
- Access reviews. These are typically performed for each application to determine who has access to what. Who has admin privileges? Are former employees still in the system? Is someone accessing business data with a personal email login? Periodic access reviews are critical to preventing future attacks.
- Compliance audit, which looks at how well your company is obeying the regulations and laws that relate to your industry. For instance, PCI compliance is required by any business that accepts credit card payments, while a defense contractor will have to adhere to Cybersecurity Maturity Model Certification (CCMC) compliance. Compliance audits review your business as well as any external vendors.
What are co-managed IT services (also called hybrid IT services)?
Co-managed IT services (or hybrid IT services) are when you use a managed service provider (MSP), to supplement your in-house IT staff. Larger businesses that can maintain an internal IT team often find that co-managed services are the best of both worlds: You decide what tasks to keep in-house and how to best leverage the MSP resources.
Here are a few examples of how hybrid IT services could work:
- Your in-house IT team runs your help desk and handles day-to-day maintenance, but leans on the expertise of your MSP for cyber security, as well as general advice and assistance.
- Your MSP acts as your CIO (sometimes called virtual chief information security officer or VCISO services). Your in house team executes plans and manages your systems.
- Your in-house IT lead handles the strategy but directs an outsourced managed IT team to execute plans and support the larger team.
Are there cloud computing benefits for small business?
Cloud computing benefits for small business include:
- Flexibility. Cloud computing expands your technological infrastructure resources as needed. No need to plan ahead and figure out how much data storage will you need in a year or how many locations will need to access that data. Simply scale your cloud services to meet your needs.
- Lower costs. With cloud services you pay for what you use (usage-based pricing) and it takes fewer hours to manage your data. This also moves your infrastructure costs from CapEx (capital expenditures) to OpEx (operational expenses) because you are not buying the servers, just the space you need on them.
- Accessibility. Your users can access their work data from anywhere with an internet connection. Plus, multiple users can work on the same data at the same time.
- Less maintenance. Because cloud applications are not installed on each user’s computer, they don’t need updates and patches applied to every endpoint. All that happens on the cloud, which is why managing your data takes less time.
- Better peak load capacity. On the cloud, resources are shared across a large pool. This means peak-load capacity increases and there is more efficiency for systems that are less used.
- Redundancy. A well-designed cloud solution makes use of multiple redundant sites. That way your data and backups are protected and available even if one site is compromised.
- Security. When implemented well, cloud security is just as good as (or better) than security on traditional systems.
What is a cyber security managed service provider?
A cyber security managed service provider (also called a managed cyber security provider or MSSP) provides cyber security services as part of end-to-end IT coverage. Those services typically include:
- Proactive monitoring 24/7/365 that is looking for vulnerabilities and fixing them before they can be exploited.
- Infrastructure management, recommending specific security and productivity improvements.
- Help desk services supporting your team around the clock.
- Incident response countering attacks as they occur, often blocking them before they breach your system.
- Cyber security training that focuses on turning your entire team into human fire walls, instead of your weakest link.
With a cyber security managed service provider, these services and more are packaged into a flat rate monthly fee, so that you can better plan for meeting your company’s technology needs.
What are cyber security services providers?
In general, cyber security services providers are companies that provide cyber security to other businesses as a service. There is also a Cybersecurity Service Provider (CSSP) designation issued by the Department of Defense that specifies the knowledge and experience needed to work on DoD projects. When the acronym is used (CSSP) it is usually referring to the DoD certification. Not all cyber security services providers hold CSSP designations (or need to unless they are working for the DoD).
When companies work with a cyber security service provider, they can leverage a more robust set of security protocols and deeper expertise than they can typically afford to hire in-house. The cyber security provider runs tests to find vulnerabilities, monitors networks for intrusions and responds to any incidents. The methods used to accomplish this can vary, as can the specific services offered and the cost.
A managed cyber security service provider (MSSP) bundles cyber security services into a comprehensive managed service agreement. You still get proactive monitoring, incident response and remediation. But you also get infrastructure management, 24/7/365 help desk services, end-user security training and other managed service components — all for a flat monthly fee.
What is a cloud managed service provider?
A cloud service provider is a third-party company offering cloud-based platforms, infrastructure, applications and storage services. You pay for the service based on how much you use. Think of this like renting a loft apartment. It’s the space you are buying — how you arrange the living space and get your belongings moved in is your responsibility.
A cloud managed service provider bundles those cloud services into a managed service agreement. That means you are not just buying the services, but also getting the expertise and support you need to keep it secure and optimized. Going back to that rental loft, the cloud managed service provider doesn’t just sell you the space, they configure the space to best meet your needs, move you in and then stick around to help keep the place clean and secure.
What is a managed service provider?
A managed service provider (MSP) provides IT support and consulting for a predictable monthly fee. That support includes 24/7/365 proactive network monitoring, IT infrastructure management, cyber security, help desk services and more. It’s “managed” because the MSP is proactively working to keep your network free of issues, not just fixing what breaks. A good MSP partners with you to get the most productivity out of your business and team with the right technology.
Of course, there’s a lot more to it than that simple definition. It’s a complex job to monitor and protect all your endpoints, data and infrastructure as well as to provide technology leadership guidance. The best IT providers also train your entire team to avoid phishing and prevent cyber attacks.
What is IT project outsourcing?
IT project outsourcing is when you hire a vendor or contractor to take on a specific IT task, usually with a fixed time frame and scope. Common IT projects that are outsourced include server migrations (e.g., from on premise server to the cloud), email migrations (e.g., from G-Suite to Microsoft 365) or integrating multiple systems together.
Many times, a company’s first outsourcing experience is with IT project outsourcing. A need comes up that their internal IT team doesn’t have the expertise or bandwidth to resolve and outsourcing the project is a natural solution. Most managed service providers also provide IT project outsourcing, although some will only do so for existing managed clients. It’s not uncommon for a company to decide to sign up for managed services after a positive experience with an IT project completed by an MSP.
What is IT help desk outsourcing?
IT help desk outsourcing is when you hire an external vendor to provide your IT help desk (the place your team, and sometimes your customers, go for technical support related to your network). A managed service provider offers help desk services as a part of a comprehensive technology solution. But the term “IT help desk outsourcing” typically refers to outsourcing for only help desk support, not as part of a managed solution.
Help desk technicians take calls, emails, chat sessions or tickets then do their best to fix the user’s immediate problem. IT help desk services typically involve:
- Running system diagnostics.
- Making changes to computer hardware and software, including installing or making repairs.
- Escalating the problems to a more expertised tech if they are unable to solve it.
- Following-up with the user to ensure that issues have been resolved.
Your managed service provider help desk will perform all these tasks as well. The difference is that your help desk team is part of a larger team actively working to prevent issues on your network. That means they are already extremely knowledgeable about your business and IT infrastructure. The team you work with from a standalone help desk outsourcing provider usually does not have the same level of insight into your business or the ability to help prevent similar issues from arising in the future.
What is meant by the outsourcing of IT services?
Outsourcing is when you hire an external resource for a specific business function instead of hiring an internal staff member or team. So, the outsourcing of IT services is simply hiring an external vendor to fulfill some or all of your IT needs. This can take a couple of forms:
- “Break fix” IT support: IT services that may include paying per hour for support or buying a certain number of hours per month. They’re designed to fix a problem or fill a specific need that arises. They are NOT proactively finding potential issues and preventing them from impacting your business.
- Managed IT services: An end-to-end IT solution, including a team actively working to keep your network free of problems 24/7/365. When you outsource your IT support to a managed service provider (MSP), you get the benefit of a large, experienced and highly efficient IT team working to prevent outages or breaches. Plus, it typically costs less per month than a single in-house staff member, much less an entire team. The best MSPs offer flat-rate predictable pricing and all-inclusive services customized for your business.
Contact us to learn more about how the outsourcing of IT services can help your business.
Use our Checklist to Find IT Support
Are you a first-timer to IT support? Maybe you aren’t happy with your current MSP? Our easy-to-follow checklist can guide you through the process of the best IT services provider for your business. It will help you help you outline and define:
- Your business goals for the next few years
- The stats that potential MSPs will need to work out a plan for your company
- The risk areas in your backup and cyber security practices
- What you expect from your IT support provider
- And more!
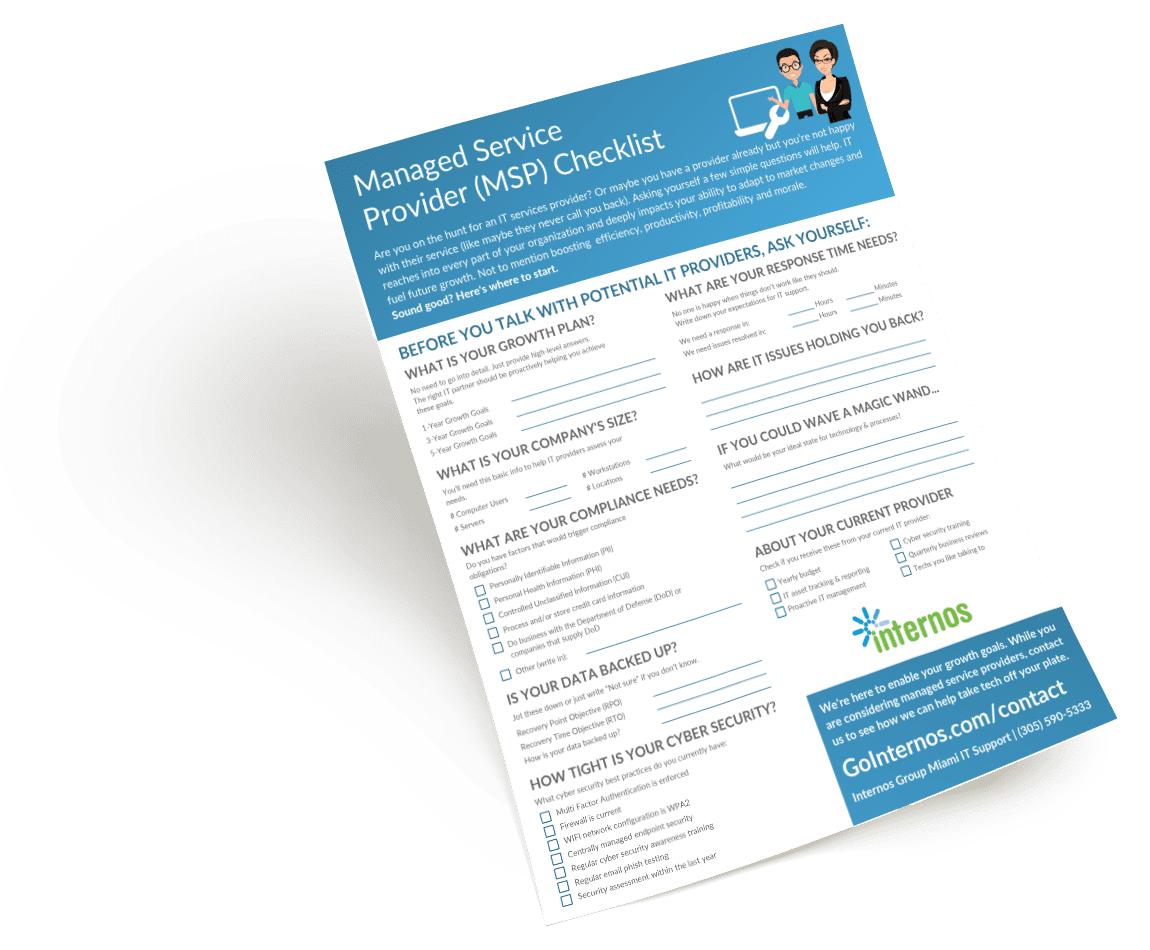
Download the Checklist
The "Get Done" Business Plan
Book a no-obligation consultation.
Rely on our project services.
Feel unleashed to succeed.
