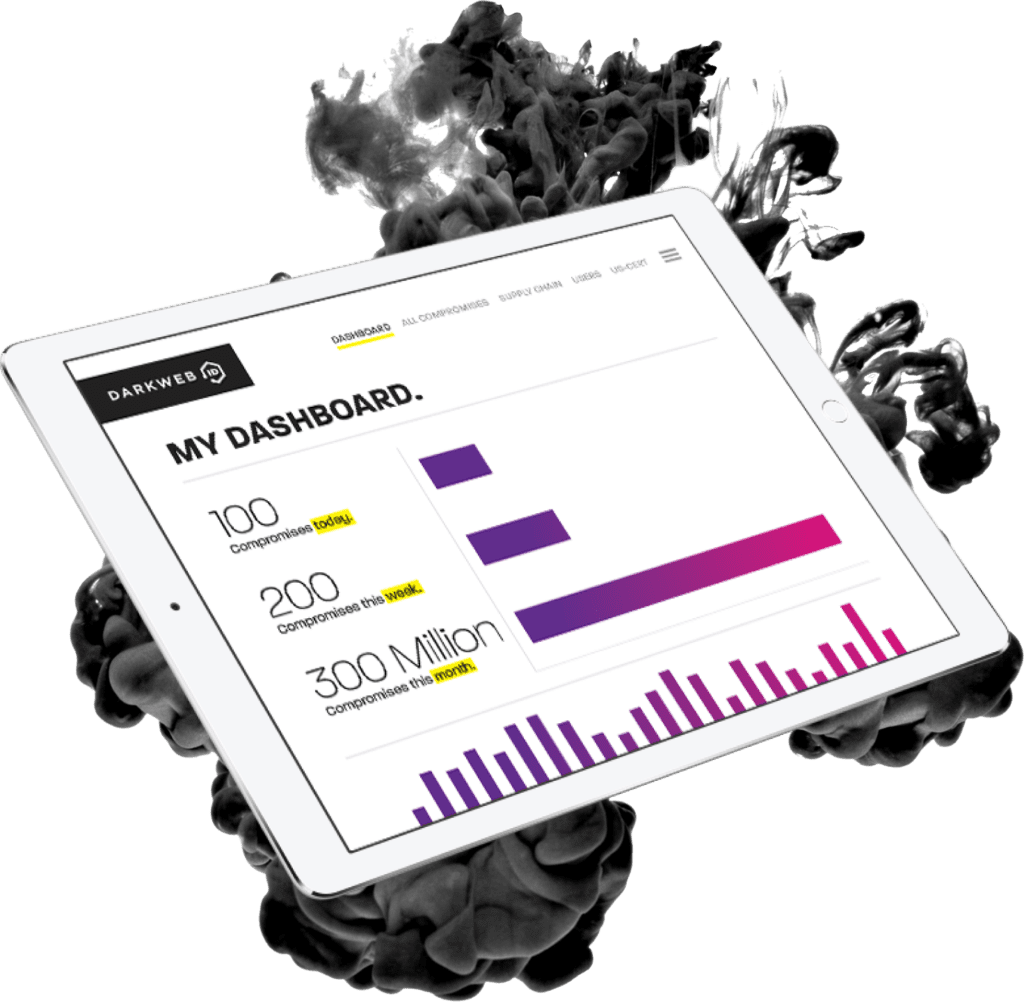
Prevent a major breach
Monitor 27/7/365
Identify compromised credentials
Track and triage incidents
Predict industry patterns
81%
of hacking-related breaches that leverage either stolen or weak passwords
60%
of small businesses go out of business within six months of a cyber incident
43%
of cyber attacks target small businesses
over75%
of compromised credentials are reported to the victim’s organization by a third party, such as law enforcement. They are NOT discovered by the organization itself.
What Is the Dark Web?
The dark web is made up of digital communities that sit on top of the internet, and while there are legitimate purposes to the dark web, it is estimated that over 50 percent of all sites on the dark web are used for criminal activities, including the disclosure and sale of digital credentials. Far too often, companies that have had their credentials compromised and sold on the dark web don’t know it until they have been informed by law enforcement, but by then, it’s too late.
How Does Dark Web Monitoring Work?
By using a combination of human and sophisticated dark web intelligence with search capabilities, dark web monitoring is able to identify, analyze and proactively monitor for your organization’s compromised or stolen employee and customer data. It looks at:
- Hidden chat rooms
- Private websites
- Peer-to-peer networks
- IRC (internet relay chat) channels
- Social media platforms
- Black market sites
- 640,000+ botnets
Employees often use the same password for multiple services, exponentially increasing the potential damage from a single compromised credential.
Request a Free Dark Web Scan
Qualified businesses in our Miami / Fort Lauderdale service area can get a free preliminary dark web scan with analysis from the Internos team. Complete the form to request your scan.