You know MFA is the right move for your business. But how do you smoothly roll out a multi factor authentication set up for your team? As with any change, there will be some resistance. Here is an action plan to help you push past people’s fear to get up and running.
- Start with the IT team, whether it is an internal team or an MSP. Set the goal of rolling out MFA across your networks and systems for all users.
- Include training and support. The rollout plan should include end-user training and support for the entire team. You want to roll out MFA without stressing your team or impacting productivity. The only way to do that is with empathy and training. People using MFA for the first time will feel a bit like learning a foreign language. Training will help them understand why it is important. Ongoing support will help them become comfortable with the new protocols.
- Include your vendors and partners. Each should be required to enable MFA as well. Consider switching vendors if any don’t offer MFA security.
- Monitor invalid access attempts. This data can be used to improve your cyber security.
- Plan for immediate lockout support. People who are locked out or unable to authenticate should get the help they need fast, otherwise people will try to “work around” the system. Lockout support will help ensure that your MFA rollout has as little impact as possible on productivity.
You don’t have to go it alone. Many small and medium sized businesses need help with multi factor authentication set up from a trusted IT partner. Even companies with in-house IT teams find it helpful to have an MSP train teams and monitor access attempts.
For this or any other business IT questions, contact us or book a meeting. We’re here to help.
View all FAQs
A vulnerability is a weak spot in a system. Vulnerabilities enable hackers and crackers to gain access to a network. It is virtually impossible to have no weak spots, and not all weak spots exist inside the code itself. The biggest vulnerability for many companies is people. Human examples of vulnerabilities include a human response…
A zero day attack happens when a hacker takes advantage of an unpatched or previously unknown vulnerability for the first time (also known as a zero day vulnerability). Some examples of zero day exploits include: Critical system vulnerabilities and exposures are tracked by some organizations and websites to distribute to others. They maintain lists of…
There are multiple benefits associated with IT service management, including: Aside from the benefits above, the day-to-day conveniences of using an ITSM are many. ITSM is not just support via a help desk or a service desk. While an ITSM may support your business via a service desk, the offerings are much broader than that….
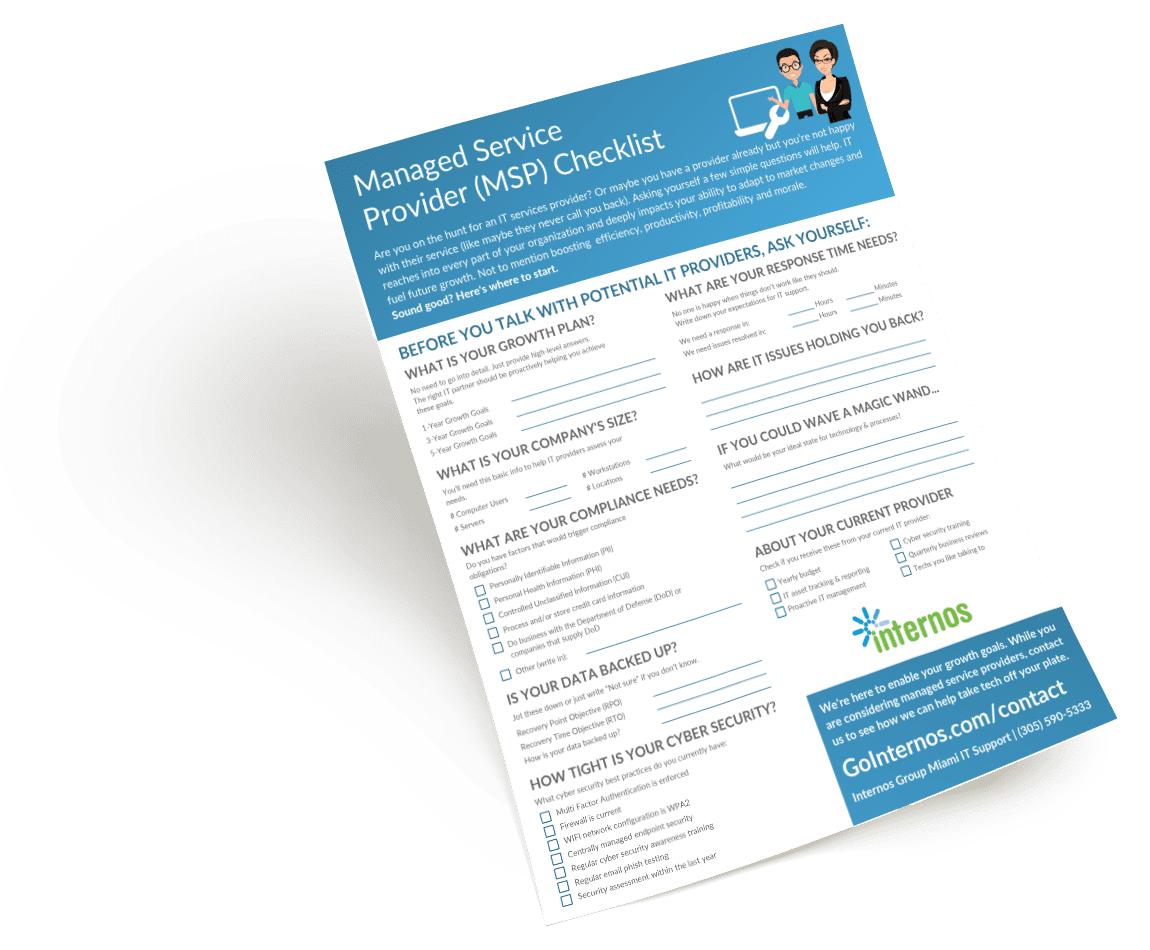
Use our Checklist to Find IT Support
Are you a first-timer to IT support? Maybe you aren’t happy with your current MSP? Our easy-to-follow checklist can guide you through the process of the best IT services provider for your business. It will help you help you outline and define:
- Your business goals for the next few years
- The stats that potential MSPs will need to work out a plan for your company
- The risk areas in your backup and cyber security practices
- What you expect from your IT support provider
- And more!