Managed IT service providers come in all shapes and sizes, from the “guy in his garage” to large national firms. So, finding one won’t be a problem. But you can’t just choose any managed service provider. It’s important to find a quality IT partner for your business Here is what to look for:
- 24/7/365 monitoring and support
- Fast response times (e.g., “We’re working on it”) and reasonable resolution times (e.g., “We’re done”) based on the level of impact the issue is having on your business
- Experience with your business, industry, environment and/or requirements — and client references to back it up
- High average customer satisfaction ratings (CSAT) and client references to back them up
- Actually located within the Miami or South Florida area (not simply a local address to attract businesses). Your MSP should provide services in your offices when needed and not just remotely. Even better, they’ll schedule regular onsite visits to train staff or review equipment.
- No long-term contracts. A top MSP doesn’t need to lock you into a long-term contract because they will earn your business month after month with exceptional service. You should be able to cancel all or part of your IT services with 30 days notice.
These are just the basics, but they should help whittle down your list. Then you need to learn about each potential MSP’s specific IT processes and protocols. Get more questions to ask or download our Choose IT Support checklist.
View all FAQs
A vulnerability is a weak spot in a system. Vulnerabilities enable hackers and crackers to gain access to a network. It is virtually impossible to have no weak spots, and not all weak spots exist inside the code itself. The biggest vulnerability for many companies is people. Human examples of vulnerabilities include a human response…
A zero day attack happens when a hacker takes advantage of an unpatched or previously unknown vulnerability for the first time (also known as a zero day vulnerability). Some examples of zero day exploits include: Critical system vulnerabilities and exposures are tracked by some organizations and websites to distribute to others. They maintain lists of…
There are multiple benefits associated with IT service management, including: Aside from the benefits above, the day-to-day conveniences of using an ITSM are many. ITSM is not just support via a help desk or a service desk. While an ITSM may support your business via a service desk, the offerings are much broader than that….
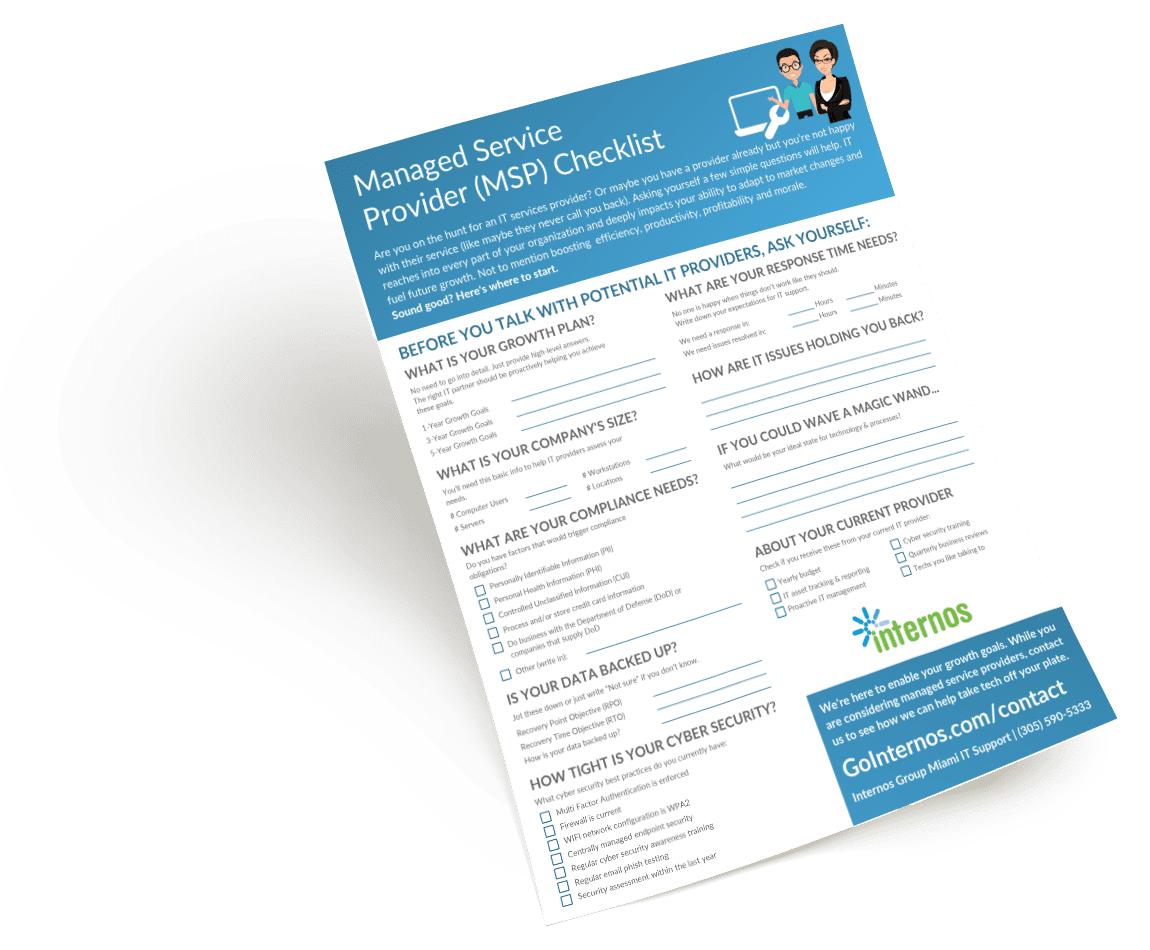
Use our Checklist to Find IT Support
Are you a first-timer to IT support? Maybe you aren’t happy with your current MSP? Our easy-to-follow checklist can guide you through the process of the best IT services provider for your business. It will help you help you outline and define:
- Your business goals for the next few years
- The stats that potential MSPs will need to work out a plan for your company
- The risk areas in your backup and cyber security practices
- What you expect from your IT support provider
- And more!