Is Your Small Business Doing Enough?
78%
of small businesses store valuable or sensitive data and do NOT encrypt that data.
81%
of small businesses only verify asset location annually (or even less often).
75%
of small business owners report NOT having a disaster recovery plan in place.
51%
of small businesses say they’re not allocating ANY budget to cyber security.
14%
of small businesses rate their ability to reduce cyber risks as “highly effective.”
62%
of small businesses report not regularly upgrading or updating their software and applications.
Is it any wonder why 80 percent of SMBs worry they’ll be a target of cyber crime within six months?
Cyber Criminals Love Small Businesses
>50%
The percentage of SMBs reporting they have been victims of cyber crime.
50%
The percentage of cyber attacks estimated to specifically target small businesses.
$133,000
The average cost of a ransomware attack for SMBs (an average data breach costs $149,000).
66 Days
The average time that passes after a cyber attack before it is detected.
Common Cyber Attack Tactics
Malicious actors have a variety of tried and true approaches to access your network, steal your data or disrupt your business. Here are just a few examples:
- Phishing: These are convincing-looking emails that contain malicious attachments or links. One click and malware is downloaded.
- DDOS (distributed denial of service): This attack targets a website, network, server or computer to take it offline and disrupt your business.
- Man in the middle (MITM): The criminals pose as a system user to you and as YOU to a system user. Those users could be people (employees, clients, vendors) or other servers and networks. With MITM, criminals can take control of sessions or spoof IPs to gain access to servers and applications.
- Malware: Ransomware gets all the press, but there are many types of malware to worry about, including viruses, worms, trojans and other infections.
- Password: Using one or more of the above tactics, criminals get your password and then use it to access your network — or bank account, if your passwords are like the 73 percent that are used for more than one site.
- Drive-by: This is a silent malware attack. It hits but then runs in the background, spying and collecting data for future attacks or to sell or ransom.
As we invent better ways to protect systems, cyber criminals create new attacks or variations to trick users and gain access. That’s why it’s important to get on the road to better protection now.
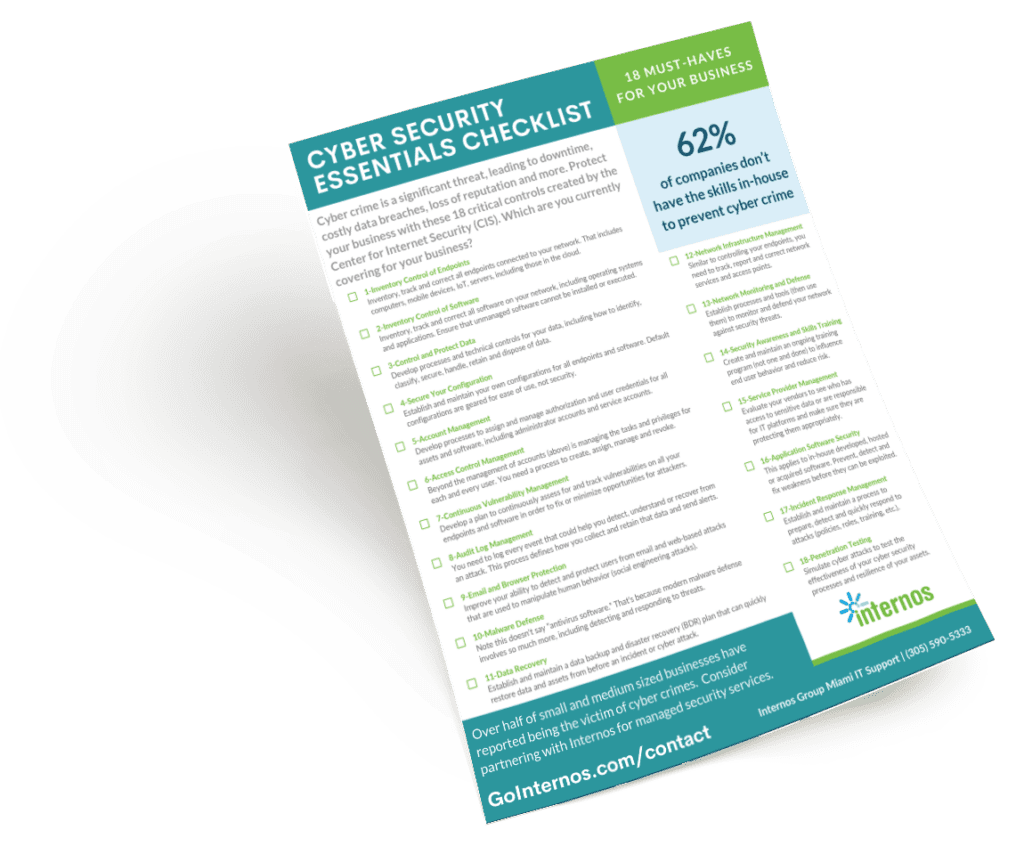
Get Your Free Cyber Security Essentials Checklist
Just complete this short form.